Next Tuesday, April 14, Magento Commerce 2.3.5 will be introduced to current Magento Commerce customers and partners only. Meanwhile, Magento Open Source 2.3.5 will become generally available (GA) on April 28th.
The new version includes many important updates to security, quality, and platform technologies. Many business activities might slow down the middle of the COVID-19 pandemic; however, let’s take this crisis as a chance to improve the technical capability of your eCommerce system.
There are over 180 functional fixes to the core product and over 25 security enhancements. Magento 2.3.5 is expected to continuously deliver a secure environment for online purchases all over the world.
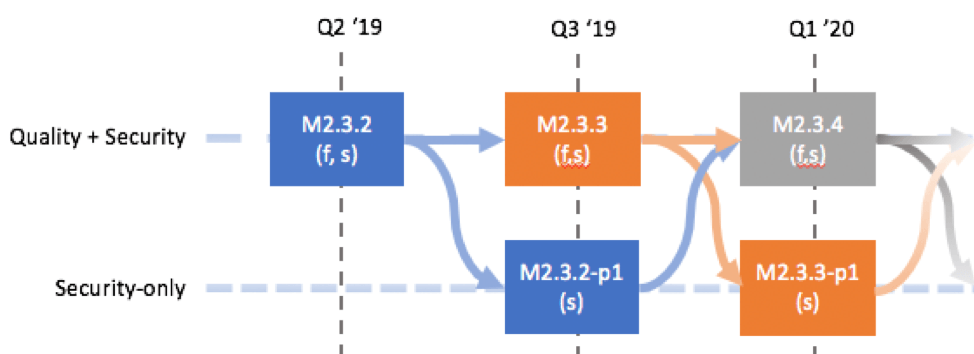
Security-only patch 2.3.4-p1
On April 14, merchants can now install time-sensitive security fixes without applying the hundreds of functional fixes and enhancements that a full quarterly release (for example, Magento 2.3.5) provides. Patch 2.3.4.1 (Composer package 2.3.4-p1) is a security-only patch that provides fixes for vulnerabilities that have been identified in Magento previous quarterly release, Magento 2.3.5 All hotfixes that were applied to the 2.3.4 release are included in this security-only patch
Highlights in Magento 2.3.5
#1 Close remote code execution (RCE) & cross-site scripting (XSS) vulnerabilities
Most of the security issues require that an attacker first obtains access to the Admin. Therefore, in order to protect your website, it’s important to take all necessary steps to protect your Admin such as IP whitelisting, two-factor authentication, use of a VPN, the use of a unique location rather than /admin, and good password hygiene. All known exploitable security issues fixed in this release (2.3.5) have been ported to 1.14.4.5 and 1.9.4.5, as appropriate.
#2 Security enhancements & fixes to core code
- Implementation of Content Security Policy (CSP). Content-Security-Policy is an HTTP response header that browsers can use to improve the security of a web page. This added layer of security supports the detection and mitigation of attacks, including cross-site scripting (XSS) and data injection attacks. This Magento 2.3.5 implements the CSP SPI, which developers can use. Report-only mode is the default.
- Removal of session id from URLs. Exposure of session id values in URLs creates a potential security vulnerability in the form of session fixation. The code is removed from the classes and methods add/read session id is also removed from URLs.
Final words
For more info about Magento 2.3.5, you can join the Monthly Magento Partner Sales and Program Update webinar that will be held on April 9 with an overview of Magento 2.3.5 and all the latest enhancements. You can register here.
If you run into any problems with the system upgrade, please contact us via support@magenest.com for assistance.